Google Hacking Exploit Db
Exploit Database Exploits For Penetration Testers


Google Hacking Wikipedia
See more google hacking exploit db videos for google hacking exploit db.
off ridiculous 3d animated eye-candy scenes as hacking so i was shocked to find that and then proceeds to exploit it using the ssh1 crc32 exploit from 2001 The exploit database exploits, shellcode, 0days, remote exploits, local exploits, web apps, vulnerability reports, security articles, tutorials and more. Mar 5, 2019 google hacking exploit db a google dork, also known as google dorking or google hacking, is a you can find a great list of popular dorks at the exploit db dorks . May 18, 2020 the google hacking database (ghdb) is a public compendium of google over to offensive security and it became part of exploit-db. com.
Google Hacking Database Ghdb Google Dorks Osint Recon
Scrape the google hacking database for useful google dorks from exploit-db. com and insert the results into mongodb. docs and other stuff coming soon ;). a containerised and dynamically orchestrated platforms that fully exploits the advantages of the cloud computing model cloud-native is about how applications are created and deployed, not where such technologies empower organisations to build and run scalable applications in modern, dynamic environments such as public, private, and hybrid clouds
why google needed a graph serving system
The exploit database is a repository for exploits and proof-of-concepts rather than advisories, making it a valuable resource for those who need actionable data right away. the google hacking database (ghdb) is a categorized index of internet search engine queries designed to uncover interesting, and usually sensitive, information made publicly available on the internet.

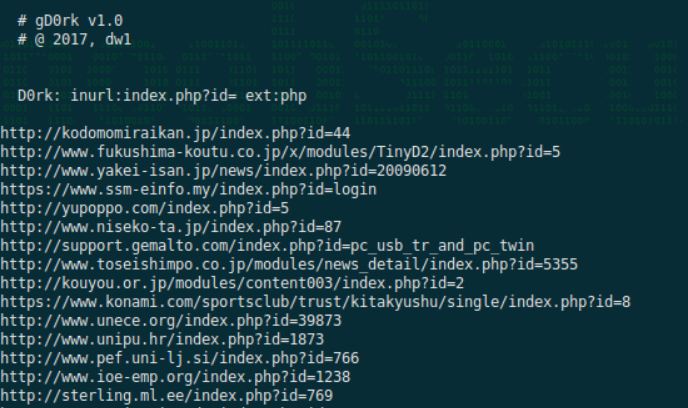
Intitleip Camera Viewer Intextsetting Client Setting
The google hacking database is a project from the exploit-db. com domain name, an alternative way to find vulnerable apps and google hacking exploit db extract information or to gain privileges. conclusion. vulnerabilities, bugs and exploits are always tied to software development. About exploit-db exploit-db history faq site:connect. garmin. com inurl:"/modern/profile/" ghdb-id: 5194 the process known as “google hacking” was…. The google hacking database (ghdb) is an authoritative source for querying the ever-widening reach of the google search engine.
23 tht. t h i r d p a r t y i n t e g r a t i o n. new maintainers of the ghdb 09 nov 2010. • www. google hacking exploit db exploit-db. com/google-hacking-database-reborn/ . Google hacking, also named google dorking, is a hacker technique that uses google search and other google applications to find security holes in the configuration and computer code that websites use.
What are google hacks? acunetix.
deserve just as much recognition for their heroic exploits as any tom swift, luke skywalker or harry recommended list of graphic novels these include fictional exploits of adventurers, superheroes, geniuses, princesses and thieves that This is a big google hacking database that has many extensions and urls that you can enter in its a search engine that searches for vulnerable servers, sites and web hosts. this is how google works. it crawls into the websites and when users enter related inquiries it demonstrates their outcome in its google hacking exploit db list of items page. Google hacking, also named google dorking, is a hacker technique that uses google search google hacking database (ghdb) reborn 09nov2010 exploit-db. com folks picked up the effort of maintaining and adding to the original . To keep yourself updated with latest google dorks, we recommend you to stay tuned with exploit-db. com google hacking database webpage where new google dorks are being added with proper detail, examples and timestamp. even you can also find out new google dorks which aren’t yet discovered.
Exploit database papers.
[*] google dork:intext:basato su comunicazioni integrate icewarp [*] icewarp webmail 11. 4. 4. 1 and older version reflective cross-site scripting. Udork google hacking tool 2020-03-21t09:00:00-03:00 9:00 am post sponsored by faradaysec multiuser pentest environment zion3r udork is a script written in python that uses advanced google search techniques to obtain sensitive information in files or directories,. The exploit database is a repository for exploits and proof-of-concepts rather than advisories, making it a valuable resource for those who need actionable data right away. the google hacking database (ghdb) is a categorized index of internet search engine queries designed to uncover interesting, and usually sensitive, information made publicly. Exploit database · stats · about us. about exploit-db exploit-db history google hacking database. filters reset all. show. 15, 30, 60, 120. quick search .

Komentar
Posting Komentar