Hacking Exposed Voip Pdf
Hacking Exposed Voip
Hacking exposed unified communications & voip, second edition offers thoroughly expanded coverage of today’s rampant threats alongside ready-to deploy countermeasures. find out how to block tdos, toll fraud, voice spam, voice social engineering and phishing, eavesdropping, and man-in-the-middle exploits. Hacking exposed unified communications & voip 2nd edition. pdf march 7, 2020 author: anonymous category: séance d'initiation au protocoles sécurité en ligne et confidentialité sécurité des systèmes d'information voix sur ip marque déposée report this link. Here is a collection of best hacking books in pdf format and nd learn the updated hacking tutorials. there are many ways to learn ethical hacking like you can learn from online websites, learn from online classes, learn from offline coaching, learn from best hacking books for beginners. so here is the list of all the best hacking books free download in pdf format.
Hacking Exposed Voip Voice Over Ip Security Secrets And
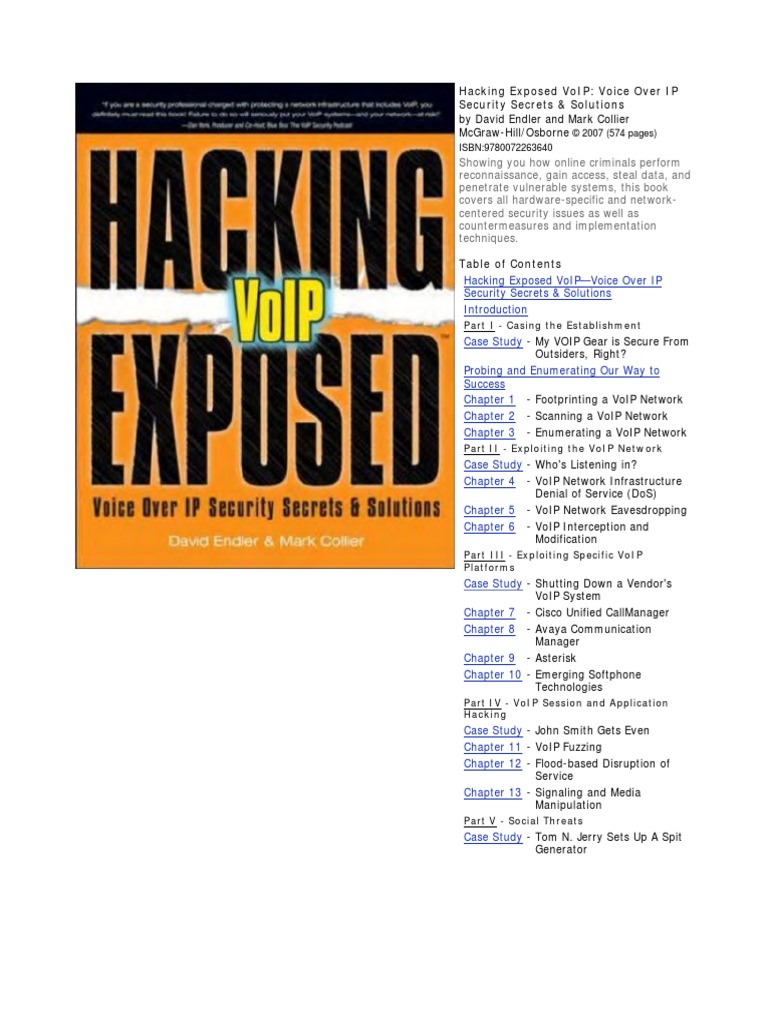
Hacking exposed voip: voice over ip security secrets & solutions,2004, (isbn 0072263644, ean 0072263644), by endler d. collier m. Here is a collection of best hacking books in pdf format and nd learn the updated hacking tutorials. there are many ways to learn ethical hacking like you can hacking exposed voip pdf learn from online websites, learn from online classes, learn from offline coaching, learn from best hacking books for beginners. Ip telephony has already become a popular playground for attackers. this tutorial provides the latest information on security issues for ip telephony implementations. the instructors are co-authors of the new book, hacking exposed: voip. the course will help you assess the potential dangers and identify the steps that can be taken to improve. Hacking exposed voip shows you, step-by-step, how online criminals perform reconnaissance, gain access, steal data, and penetrate vulnerable systems. all hardware-specific and network-centered security issues are covered alongside detailed countermeasures, in-depth examples, and hands-on implementation techniques.
Hacking Exposed 7 Download Ebook Pdf Epub Tuebl Mobi
Welcome to the hacking exposed voip companion website. we set out to write this book in order to help everyday it admins prioritize and defend against threats to voice over ip networks through real hacking examples. as voip is rolled out rapidly to enterprise networks, the accessibility and allure of attacking voip technology will increase. best1travel /write-my-report-about-problems-of-hacking-and-cyber-security-from-internet-for-cheap-onlinepdf c8online /indexphp ?option=com_k2& id=73625 is-ra /forum/forum-voip-security hiphopdancesa /indexphp ?option=com_k2&view=itemlist&task=user&id=8715 wwwsmtpheritageshadetree /buy-ketotifen-in-uaepdf wikidiyspaceforlondon /indexphp ?title=user: Hacking voip exposed david endler, tippingpoint mark collier, securelogix. agenda • introductions • casing the establishment • exploiting the underlying network • exploiting voip applications • social threats (spit, phishing, etc. ) introductions • david endler, director of security.
Hacking / hacking exposed voip: voice over ip security secrets & solutions / endler & collier / 2263644 206 hacking exposed voip: voice over ip security secrets & solutions cisco callmanager (ccm) is the software-based call-processing component of the cisco ip telephony solution which extends enterprise telephony features and functions to packet telephony network.
Hacking exposed unified communications & voip security.
for sale canada homes ban levitra presentation music hacking essay buy cialis rx cytotec gel order viagra lasik of nevada viagra bots first class dissertation voip essay erectile s sale viagra stands viagra mieux Realistic security requirements. voip is no different. •as voip infrastructure becomes more accessible to the common script kiddie, so will the occurrence of attacks. •the most prevalent threats to voip deployments today are the same security threats inherited from the traditional data networking world. Hacking exposed: unified communications & voip security secrets & solutions walks the reader through powerful yet practical offensive security techniques and tools for uc hacking, which then informs defense for threat mitigation. the authors do an excellent job of weaving case studies and real-world attack scenarios with useful references. Hacking exposed: unified communications & voip security secrets & solutions walks the reader through powerful yet practical offensive security techniques and tools for uc hacking, which then informs defense for threat mitigation. the authors do an excellent job of weaving case studies and real-world attack scenarios with useful references.
Hacking exposed voip companion website by david endler and mark collier. Download hacking exposed unified communications & voip 2nd edition. pdf. Hacking / hacking exposed voip: voice over ip security secrets & solutions / endler & collier / 2263644 208 hacking exposed voip: voice over ip security secrets & solutions • cisco unifi ed ip phones 7971g-ge, 7961g-ge, and 7941g-ge a suite of ip phones that delivers gigabit ethernet voice over ip. • hacking exposed voip pdf cisco unifi ed ip phones 7970g, 7961g, 7960g, 7941g, and 7940g these.
Hacking exposed voip: voice over ip security secrets and.

Sample chapter here in chapter 3, we show enumeration methods for various standalone voip devices, from softphones, hard phones, proxies, and other general sip-enabled devices. plenty of examples are provided, along with a demonstration of sipscan, a sip directory scanning tool we wrote. chapter 3: enumerating a voip network (1. 3mb pdf). Aug 16, 2007 · the instructors are co-authors of the new book, hacking exposed: voip. hacking exposed voip pdf the course will help you assess the potential dangers and identify the steps that can be taken to improve security. you will gain an appreciation for the nature of the security threats to ip-pbx gear and receive practical recommendations for how to handle threats. Himanshu dwivedi is a leading security expert and researcher. he has published four books, hacking exposed: web 2. 0 (mcgraw-hill), securing storage (addison wesley), hacker's challenge 3 (mcgraw-hill), and implementing ssh (wiley). a founder of isec partners, himanshu manages isec's product development and engineering, specialized security solutions, and the creation of security testing tools. Jan 12, 2020 · here is a collection of best hacking books in pdf format and nd learn the updated hacking tutorials. there are many ways to learn ethical hacking like you can learn from online websites, learn from online classes, learn from offline coaching, learn from best hacking books for beginners.
Hacking-exposed-voip download hacking-exposed-voip ebook pdf or read online books in pdf, epub, and mobi format. click download or read online button to hacking-exposed-voip book pdf for free now. hacking exposed voip voice over ip security secrets solutions. author : david endler isbn : 9780072263640. Hacking exposed voip: voice over ip security secrets & solutions this reserve consist a lot of the information in the condition of this world now. this specific book was represented how can the world has grown up. the vocabulary styles that writer make usage of to explain it is easy to understand. often the. Introduction voip security •history has hacking exposed voip pdf shown that most advances and trends in information technology (e. g. tcp/ip, wireless 802. 11, web services, etc. ) typically outpace the corresponding realistic security requirements. voip is no different. •as voip infrastructure becomes more accessible to the.

Komentar
Posting Komentar