Hacking Exposed Scada
Hacking exposed industrial control systems: ics and scada security secrets and solutions shows, step-by-step, how to implement and maintain an ics-focused risk mitigation framework that is targeted, efficient, and cost-effective. the book arms you with the skills necessary to defend against attacks that are debilitating―and potentially deadly. Hacking exposed industrial control systems: ics and scada security secrets & solutions by clint bodungen, bryan singer, aaron shbeeb, kyle wilhoit, stephen hilt get hacking exposed industrial control systems: ics and scada security secrets & solutions now with o’reilly online learning. Secure your ics and scada systems the battle-tested hacking exposedâ„¢ waythis hands-on guide exposes the devious methods cyber threat actors use to compromise the hardware and software central to petroleum pipelines, electrical grids, and nuclear refineries. hacking exposed. Hacking exposed industrial control systems ics and scada security secrets solutions ics scada hacking demo with simulation.
Hacking Exposed Industrial Control Systems Ics And Scada
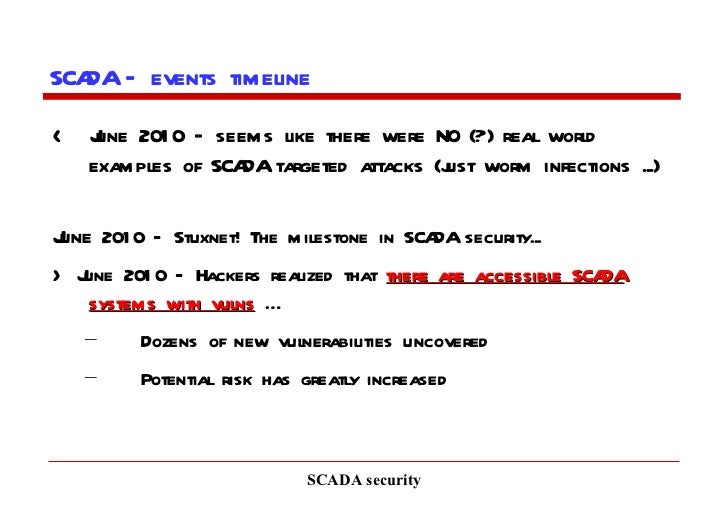
Author: clint bodungen,bryan singer,aaron shbeeb,kyle wilhoit,stephen hilt; publisher: mcgraw hill professional isbn: 1259589722 category: computers page: 544 view: 6915 download now » learn to defend crucial ics/scada infrastructure from devastating attacks the tried-and-true hacking exposed way this practical guide reveals the powerful weapons and devious methods cyber-terrorists use to. Scada system has hacking exposed scada always been an interesting target for cyber crooks, given the success of stuxnet malware that was developed by the us and israeli together to sabotage the iranian nuclear facilities a few years ago, and " havex " that previously targeted organizations in the energy sector.
Hacking exposed industrial control systems: ics and scada.
Best Software Testing Training In Noida Software Testing Training Institute In Noida
Hackingexposed industrial control systems: ics and scada security secrets and solutions shows, step-by-step, how to implement and maintain an ics-focused risk mitigation framework that is targeted, efficient, and cost-effective. the book arms you with the skills necessary to defend against attacks that are debilitating―and potentially deadly. Hacking exposed industrial control systems: hacking exposed scada ics and scada security secrets & solutions kindle edition by bodungen, clint, singer, bryan, shbeeb, aaron, wilhoit, kyle, hilt, stephen. download it once and read it on your kindle device, pc, phones or tablets. use features like bookmarks, note taking and highlighting while reading hacking exposed industrial control systems: ics and scada. Recently published by mcgraw-hill, "hacking exposed ics" follows in the same spirit as the wildly-popular "hacking exposed" series by exploring cybersecurity from an attacker's perspective. in this educational webcast, the book's lead author leverages his experience as an ics/scada security expert to show you how to implement an ics-focused risk mitigation framework that's practical and.
Ics Hacking Exposed Sans Institute


Hacking Exposed Industrial Control Systems Ics And Scada
Hacking Exposed Industrial Control Systems Ics And Scada
Hacking exposed industrial control systems: ics and scada.
Written in the battle-tested hacking exposed style, the book arms you with the skills and tools necessary to defend against attacks hacking exposed scada that are debilitating—and potentially deadly. hacking exposed industrial control systems: ics and scada security secrets & solutions explains vulnerabilities and attack vectors specific to ics/scada protocols, applications, hardware, servers, and workstations. Chapter 5 hacking ics protocols industrial protocols have evolved over time, from simplistic networks that collect information from remote devices, to complicated networks of systems that have selection from hacking exposed industrial control systems: ics and scada security secrets & solutions [book]. Hacking exposed industrial control systems: ics and scada security secrets and solutions shows, step-by-step, how to implement and maintain an ics-focused risk mitigation framework that is targeted, efficient, and cost-effective.

Learn to defend crucial ics/scada infrastructure from devastating attacks the tried-and-true hacking exposed way. this practical guide reveals the powerful weapons and devious methods cyber-terrorists use to compromise the devices, applications, and systems vital to oil and gas pipelines, electrical grids, and nuclear hacking exposed scada refineries. Learn to defend crucial ics/scada infrastructure from devastating attacks the tried-and-true hacking exposed way this practical guide reveals the powerful weapons and devious methods cyber-terrorists use to compromise the devices, applications, and systems vital to oil and gas pipelines, electrical grids, and nuclear refineries.
Hacking exposed industrial control systems: ics and scada security secrets & solutions explains vulnerabilities and attack vectors specific to ics/scada protocols, applications, hardware, servers, and workstations. Hackingexposed industrial control systems: ics and scada security secrets and solutions shows, step-by-step, how to implement and maintain an ics-focused risk mitigation framework that is targeted, efficient, and cost-effective. Hacking exposed industrial control systems: ics and scada security secrets and solutions shows, step-by-step, how to implement and maintain an ics-focused risk mitigation framework that is targeted, efficient, and cost-effective. the book arms you with the skills necessary to defend against attacks that are debilitating? and potentially deadly.
Hackers exploit scada holes to take full control of critical infrastructure. scada strangelove: zero-days hacking exposed scada & hacking for full remote control after finding more than 60,000 exposed control. training in cloud computing industrial training in ethical hacking industrial training in cad civil industrial training in cad mechnical industrial training in robotics industrial training in erp sap industrial training in embedded systems industrial training in matlab industrial training in plc scada aptron summer training in noida center summer training Book description. learn to defend crucial ics/scada infrastructure from devastating attacks the tried-and-true hacking exposed way. this practical guide reveals the powerful weapons and devious methods cyber-terrorists use to compromise the devices, applications, and systems vital to oil and gas pipelines, electrical grids, and nuclear refineries.
They probed and found holes in “popular and high-end ics and supervisory control and data acquisition (scada) systems used to control everything from home solar panel installations to critical. Secure your ics and scada systems the battle-tested hacking exposed(tm) way this hands-on guide exposes the devious methods cyber threat actors use to compromise the hardware and softw secure your ics and scada systems the battle-tested hacking exposed (tm) way. Hacking exposed industrial control systems: ics and scada security secrets & solutions explains vulnerabilities and attack vectors specific to ics/scada protocols, applications, hardware, servers, and workstations. you will learn how hackers and malware, such as the infamous stuxnet worm, can exploit them and disrupt critical processes, compromise safety, and bring production to a halt.

Komentar
Posting Komentar